Dr. Ben Goertzel, CEO of the Artificial Superintelligence (ASI) Alliance, told BeInCrypto his team can recreate the quantum attack circuits that Google Quantum AI built but refused to publish. He warned that if his organization can do it, nation-states already can too.
Google’s March 30 whitepaper showed that two working circuits implementing Shor’s algorithm to break 256-bit elliptic curve cryptography could be built with fewer than 500,000 physical qubits. The team chose not to release the code and instead published a zero-knowledge proof. Goertzel told BeInCrypto that decision changes nothing.
“Keeping Capabilities Secret Buys You at Most a Very Short Window”
Google framed its decision to withhold the circuits as responsible disclosure. The blog post called it a deliberate departure from the team’s historical practice of full transparency, motivated by the potential for misuse.
The crypto industry largely debated whether this aligned with its founding principle of “don’t trust, verify.”
Goertzel did not share the concern. He told BeInCrypto the secrecy is functionally irrelevant.
We are confident that we could regenerate the ‘secret circuit’ Google found using our own expertise and reasonable compute, and if we can do it, the Chinese government and other well-resourced actors certainly can too. Keeping capabilities secret buys you at most a very short window.
He added that the ASI Alliance has not withheld any of its own code for safety reasons, though the team has discussed it internally. His default position is openness.
The security benefits of decentralized scrutiny, he argued, outweigh the marginal risk reduction of secrecy when parallel discovery is the norm.
He did leave room for exceptions. If something posed a specific, acute, short-term danger, the team would hold it back.
But Google’s circuit, in his view, does not meet that bar because the knowledge to build it is already widely accessible to capable actors.
The 41% Problem
The Google whitepaper models what it calls an “on-spend attack.” A quantum computer could prepare part of the calculation in advance, then crack a Bitcoin (BTC) transaction in about nine minutes once the public key is exposed.
Since Bitcoin’s average block confirmation takes 10 minutes, the attacker has a roughly 41% probability of finishing first.
The paper also estimates that roughly 6.9 million BTC are already held in wallets whose public keys have been exposed in some form.
That includes about 1.7 million coins from the network’s earliest years, as well as additional funds affected by address reuse and Bitcoin’s Taproot upgrade, which makes public keys visible by default.
Goertzel told BeInCrypto that a 41% attack rate is not a borderline risk. It is a structural failure.
Any attack success rate above single digits is deeply problematic for a store-of-value chain. Once rational actors believe there is a meaningful probability that a transaction can be reversed or an address drained during the confirmation window, the game-theoretic assurances that underpin Bitcoin’s security model collapse. At 41%, you are well past the threshold.
He noted that the hardware to execute such an attack does not yet exist. But the mathematical proof is complete, and Google has set a 2029 deadline for the industry to migrate to post-quantum cryptography (PQC).
Bitcoin currently has no coordinated upgrade roadmap to meet that deadline.
ASI Alliance Says It Was Built for This
While much of the industry debated the implications, Goertzel told BeInCrypto his team saw this coming years ago.
He has previously predicted that human-level artificial general intelligence (AGI) could arrive around 2027 or 2028.
Google’s quantum timeline puts both breakthroughs on a collision course, and Goertzel said the ASI Alliance designed its infrastructure for exactly that convergence.
The convergence of AGI and quantum computing is very real, but framing it as purely a ‘threat’ misses the other half of the picture. At the ASI Alliance we have been designing ASI:Chain from the ground up to be quantum-oriented–not just quantum-resistant but quantum-leveraging…So for us, quantum computing arriving alongside AGI is a feature, not a bug.
ASI:Chain, the layer-1 blockchain under development by the Alliance, uses MeTTa as its smart contract language instead of Solidity.
According to Goertzel, MeTTa includes quantum-type systems, and the team has developed quantum versions of core Hyperon AGI algorithms covering attention allocation, probabilistic logic, and evolutionary learning.
The encryption layer is modular. Quantum-safe cryptographic primitives, including lattice-based and hash-based schemes, can be plugged in without redesigning the chain or requiring a hard fork.
The cost is computational overhead, which Goertzel called a real engineering challenge but not an architectural one.
The Artificial Superintelligence Alliance (FET) was formed through a token merger of SingularityNET, Fetch.ai, Ocean Protocol, and CUDOS.
Ocean Protocol later exited the merger, a move that later triggered legal action amid token theft allegations.
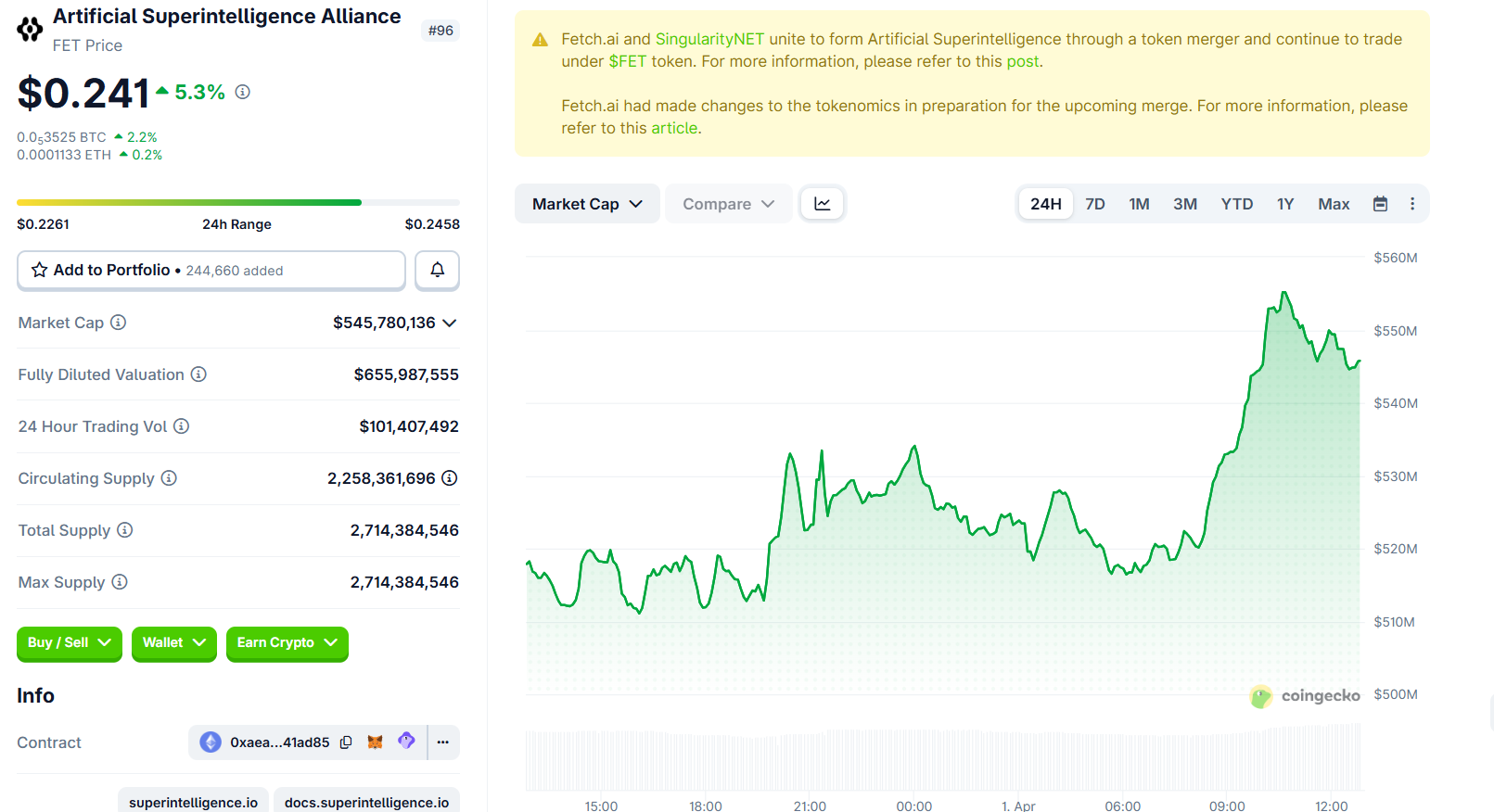
Its token, FET, currently trades at roughly $0.241, up by over 5% in the last 24 hours.
“A Catastrophic Precedent for Digital Property Rights”
Google’s whitepaper flagged roughly 1.7 million BTC in Satoshi-era Pay-to-Public-Key (P2PK) wallets that permanently expose their public keys.
These coins cannot be migrated. Their owners are either gone or unreachable. The paper proposed a “digital salvage” framework that could give governments legal authority to quantum-crack dormant coins.
Goertzel rejected the premise.
On principle, no–giving governments a legal pathway to crack private wallets sets a catastrophic precedent for digital property rights. The entire value proposition of crypto rests on the idea that your keys are your coins. Once you establish that a sufficiently powerful actor can legally seize coins whose owners are absent, you have undermined the foundation.
He acknowledged that those coins will eventually be cracked by someone. The question is whether a legal framework governs the process or it becomes a free-for-all. He leans toward leaving dormant coins untouched as a matter of principle, with the ecosystem pricing in their eventual vulnerability.
Binance co-founder Changpeng Zhao (CZ) offered a different view, suggesting that if Satoshi’s coins do not move within a certain period, the community might consider locking or burning those addresses before hackers can reach them.
He added that identifying all of Satoshi’s addresses without confusing them with early holders would itself be a challenge.
The Race Is Already On
Venture capitalist Chamath Palihapitiya called Google’s paper “quite reasonable” and urged the crypto community to organize a quantum-resistance roadmap within the next few years.
CZ said crypto would survive the quantum era but warned that coordinating upgrades across decentralized networks would spark debates, forks, and potentially new security bugs.
Goertzel’s position is blunter. He told BeInCrypto the projects that survive will be the ones that started engineering for quantum years ago. The ones that start after the first coins get cracked will not make it.
Against this backdrop, his advice for retail holders is practical. Move holdings to addresses using the most recent key formats available.
For Bitcoin, that means native SegWit (bech32) addresses where the public key stays hidden until spending. Avoid reusing addresses. For Ethereum (ETH), the vulnerability is more structural, and individual-level options remain limited.
When asked whether the quantum threat kills the decentralization thesis entirely, Goertzel told BeInCrypto that it does not.
But it raises the stakes enormously. If a centralized actor cracks dormant Bitcoin and captures hundreds of billions in assets, that becomes a massive centralizing force. The thesis, however, was never premised on legacy cryptography lasting forever.
The decentralization thesis survives if decentralized projects out-engineer centralized ones on the quantum transition. That is exactly what we intend to do.
Google’s paper, combined with a separate Caltech and Oratomic study showing Shor’s algorithm can execute at cryptographic scale with 10,000 qubits, suggests the preparation window is shorter than most assumed.
Goertzel claims his team is already on the other side of that window. The rest of the industry is now racing to catch up.
The post ASI Alliance Can Rebuild Google’s Secret Quantum Circuit, CEO Ben Goertzel Says appeared first on BeInCrypto.